CRA Compliance for Manufacturers: How the EU Cyber Resilience Act Is Reshaping Product Security
From Physical Safety to Cybersecurity
Cybersecurity isn’t optional anymore; it is as critical as physical safety. We are surrounded by billions of connected devices such as smart watches to industrial sensors in our lives. Just one security gap can trigger a chain reaction, disrupting homes, businesses, and global operations. That’s exactly why the European Union (EU) introduced the Cyber Resilience Act requirements to make sure security comes built-in, not as a last-minute patch.
From my experience working with enterprises, I’ve learned that traditional IT defenses fall short. IoT devices often bypass perimeter security, and open doors to risk we couldn’t have imagined a decade ago.
Real-world breaches prove that the attackers stop the connected smart treadmill’s(4) belt mid-run, creating physical harm. Similarly, security tests on popular baby monitors(5) uncovered serious flaws that strangers could actually tap into live video streams, turning what should be a safe space into a privacy nightmare for families. These examples highlight why CRA’s lifecycle approach is critical, not just for individual devices but for entire ecosystems.
The Cyber Resilience Act Requirements
Leaving vulnerabilities in connected products is like leaving your front door unlocked for attackers. That’s why the CRA(2) sets mandatory cybersecurity requirements for all products with digital elements, both hardware and software(6), covering almost every connected device except those already regulated (like medical or automotive). The Cyber Resilience Act mandates CRA compliance for manufacturers. The Cyber Resilience Act mandates CRA compliance for manufacturers. Products must be secure by design and by default, with all known vulnerabilities fixed before launch to protect consumers and prevent large-scale risks.
Cyber Resilience Act Requirements as the Cybersecurity Benchmark
If ISO sets the benchmark for quality and safety, CRA does the same for cybersecurity making sure connected products are secure by design and by default. It flips the old approach so that security isn’t something you tackle later; it’s baked in from day one. If your product meets Cyber Resilience Act requirements, it earns the CE mark. (1) (2) For customers, that mark says, “This product is secure and trustworthy.”
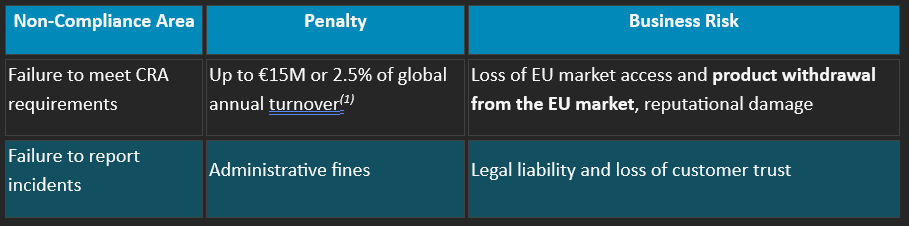
This highlights CRA’s robust enforcement measures, which mandate compliance through strict penalties and potential market withdrawal for non-conforming products.
Why It Matters: The Domino Effect Across Supply Chains
One overlooked vulnerability can disrupt entire ecosystems. Unpatched flaws cascade through Information Technology (IT) and Operational Technology (OT) environments, halting production, logistics, and critical infrastructure. For example, A compromised industrial IoT sensor could manipulate readings, stop processes, or damage machinery by impacting suppliers and customers.
The European Commission warns “A cybersecurity incident in one product can impact the entire supply chain.” With ransomware striking every 11 seconds and cybercrime costs soaring, CRA enforces security at the product level to break this chain. (6)
Here’s what CRA expects from manufacturers:
- Security support for the expected product lifetime or five years, whichever is shorter
- Patch vulnerabilities quickly to reduce exposure
- Report exploited flaws to ENISA within 24 hours from awareness(3)
These simple rules have a big impact, protecting consumers and building trust.
Impact on Manufacturers and Consumers
Manufacturers of smart gym equipment, wearables, and connected apparel are already adapting to CRA compliance for manufacturers. In one engagement, we assessed a manufacturer’s security posture, reviewing third-party components like heart-rate sensors and Bluetooth modules to avoid hidden vulnerabilities aligning with Article 14’s due diligence requirement. This revealed not just technical gaps but how vulnerabilities impact safety, privacy, and trust, making security a core design principle. For consumers, Cyber Resilience Act requirements ensure connected products remain secure long after purchase, reducing risks of data breaches, privacy violations, and physical harm.
Wearable devices and their CRA security requirements
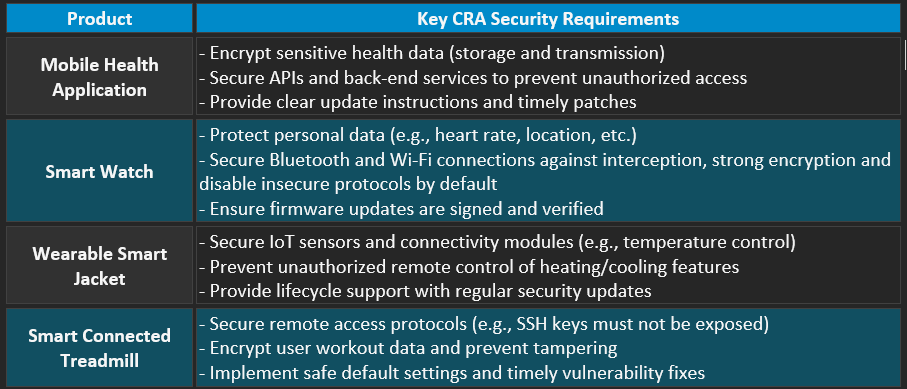
These practices were once rare in consumer tech, but now they are the standard under CRA, setting a new benchmark for digital product security.
Navigating the CRA Adoption Journey
Meeting Cyber Resilience Act requirements is not just about regulatory compliance; it represents a shift in how product security is approached. For manufacturers, CRA adoption goes beyond meeting mandatory obligations and requires a strategic transformation in the way security is designed, implemented, and sustained. Integrating security from the earliest design stages through deployment is considered a best practice, supporting a lifecycle-driven approach to resilience. This journey typically involves building organizational awareness, identifying security gaps, prioritizing risks, and implementing security controls that remain effective throughout the product’s lifecycle. For smaller businesses, cost and resource constraints are real challenges, which can be addressed through pragmatic planning, phased implementation, and informed decision-making, without compromising security outcomes.
To ease adoption, the EU offers support:
- ENISA’s guidance on CRA implementation(3)
- European Vulnerability Database for proactive risk management
- Harmonized standards mapping by ENISA and Joint Research Center, aligning CRA with existing frameworks
These initiatives help manufacturers integrate CRA obligations—secure design, vulnerability management, and incident reporting, without reinventing the wheel.
From Compliance to Competitive Advantage
The CRA sets strict rules such as risk assessments, patching vulnerabilities, and reporting incidents. However, here’s the upside for companies that embrace these requirements. They don’t just stay compliant; they stand out. A CRA-compliant product screams trust. It opens doors to:
- Security as a Selling Point: CRA-certified products signal trust and safety
- Global-Readiness: Aligns with emerging regulations, easing market entry
- Continuous Monitoring: Real-time security dashboards add value and meet CRA obligations
- Brand Trust: Security-by-design builds lasting customer confidence
Conclusion
The Cyber Resilience Act signals a clear change in how connected products are expected to be built and maintained. Security is no longer something that can be added later or handled through isolated fixes; it must be part of the product from the very beginning and carried through its entire lifecycle. While the requirements may seem demanding, they reflect the realities of today’s interconnected world, where weaknesses in one product can affect many others. For manufacturers, approaching the CRA with a practical, risk-based mindset helps turn compliance into a structured way of building trust, reliability, and long-term resilience into digital products.
References
1. Regulation (EU) 2024/2847 of the European Parliament and of the Council on Horizontal Cybersecurity Requirements for Products with Digital Elements (Cyber Resilience Act), European Union, Official Journal of the European Union, 2024, https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=CELEX%3A32024R2847
2. Regulation (EU) 2024/2847 (Cyber Resilience Act) – Official Journal Version, European Union, Official Journal of the European Union, 2024, https://eur-lex.europa.eu/eli/reg/2024/2847/oj/eng
3. European Union Agency for Cybersecurity (ENISA) – Cyber Resilience Act and Product Security Guidance, European Union Agency for Cybersecurity (ENISA), European Union, 2024, https://www.enisa.europa.eu/
4. Internet-Connected Treadmill Vulnerabilities Discovered, IBM X-Force, Security Intelligence, 2020, https://securityintelligence.com/x-force/internet-connected-treadmill-vulnerabilities-discovered/
5. Baby Beware: Critical Security Flaws Found in Smart Baby Monitors, Euroconsumers, 2019, https://www.euroconsumers.org/baby-beware-critical-security-flaws-found-in-smart-baby-monitors/
6. Cybercrime Damages $6 Trillion by , Steve Morgan, Cybersecurity Ventures, 2020, https://cybersecurityventures.com/cybercrime-damages-6-trillion-by-2021/
